Ex-presidential hopeful Tan Kin Lian exposed his own data and refuses to blame himself after getting harassed


Believing that the dangers of getting one’s personal information leaked are non-existent, Tan Kin Lian sought out to prove it.
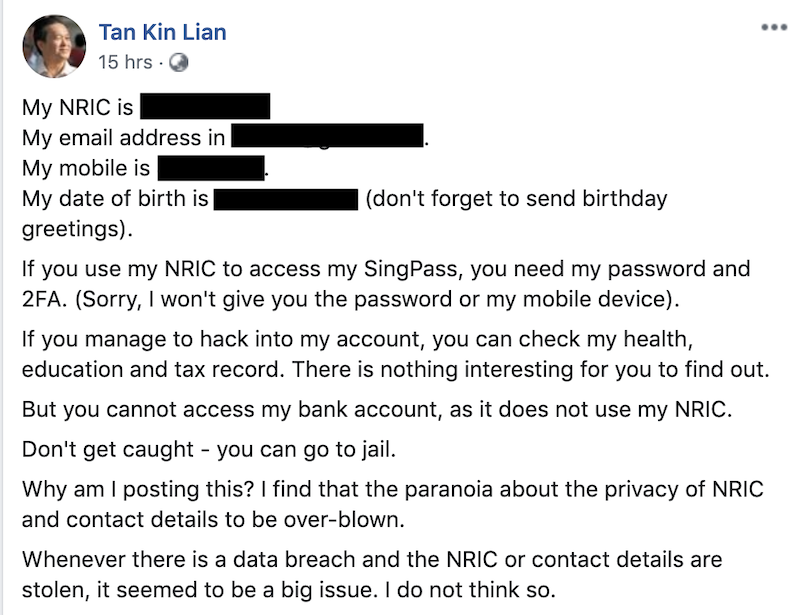
“I find that the paranoia about the privacy of NRIC (National Registration Identity Card) and contact details to be overblown,” he wrote on Facebook yesterday, expressing how he doesn’t see any troubling issue with data leaks.
The former presidential candidate laid bare all his confidential details on Facebook: his NRIC number; email address; mobile number, and date of birth. This made a lot of his detractors chuckle at what was widely regarded as a bad move.
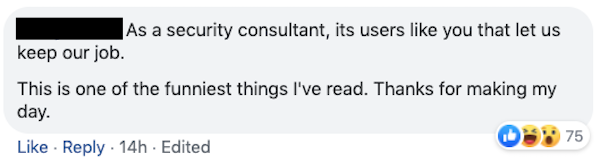
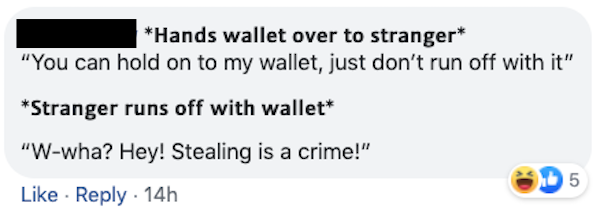
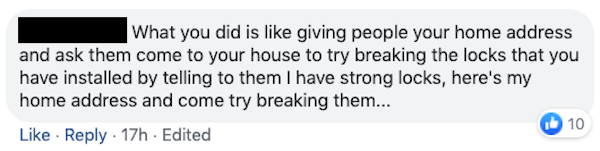
On top of that, he dared anyone to hack into his SingPass account — his personal centralised account used to access various important government e-services. Truly, Tan refused to believe that anyone could do anything criminal with his personal data.
Cut to nearly seven hours later, and Tan learned why he shouldn’t have done so. He was locked out of his own SingPass account because someone entered (probably intentionally) the wrong password way too many times.
Even if he does eventually regain control of his account by changing his password, the cat’s out of the bag — some troll could always disrupt his access again by making repeated failed attempts to log in using his NRIC number.
Though the 71-year-old had no one else to blame but himself, Tan asserted that it was “stupid” to have a maximum of six failed log-in attempts.
“I do not see how they can make SingPass secure by locking out people unnecessarily,” he wrote, totally oblivious to the fact that he brought it on himself.
In the end, Tan had no choice but to change his SingPass login ID to something else other than his NRIC number. He wrung his hands over having to change his log-in details, again oblivious to the fact that (1) he opened himself up to attacks and (2) there are password managers that can keep all his passwords under one roof.
A series of Facebook posts this morning by Tan continued to pin the blame on GovTech for their account lockout policy as he remained adamant that it should not be the case. What he doesn’t seem to understand is that account lockout thresholds are required for security because of something called a Brute Force Attack, in which hackers use bots to aggressively repeat attempts in trying various password combinations to break into accounts.
Fortunately for him, someone used a bot for less nefarious (but still annoying) purposes. According to Tan, his email was registered to about 200 mailing lists. He also had to deal with multiple requests to change the passwords to his various social media accounts.
If that’s how people are messing with his SingPass account, one can only imagine what they’re doing (or planning to do) with his contact number.
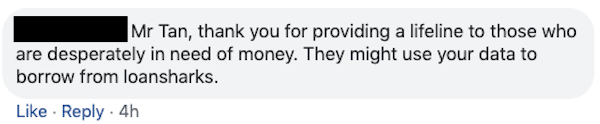
With his mobile phone number, anyone could call up his phone’s network carrier; impersonate him; answer some questions regarding his NRIC number or date of birth (both of which Tan has readily provided); ask customer service to reroute the phone number to a different SIM card; profit by receiving two-factor authentication messages and resetting passwords on all accounts associated with the phone number.
And that’s just one simple scenario about the dangers of data leaks. If anything, Tan just conducted a free masterclass in what not to do with one’s personal data.
ilyas@asiaone.com